Keeping the gate locked on your IoT devices: Vulnerabilities found on Amazon's Alexa - Check Point Research

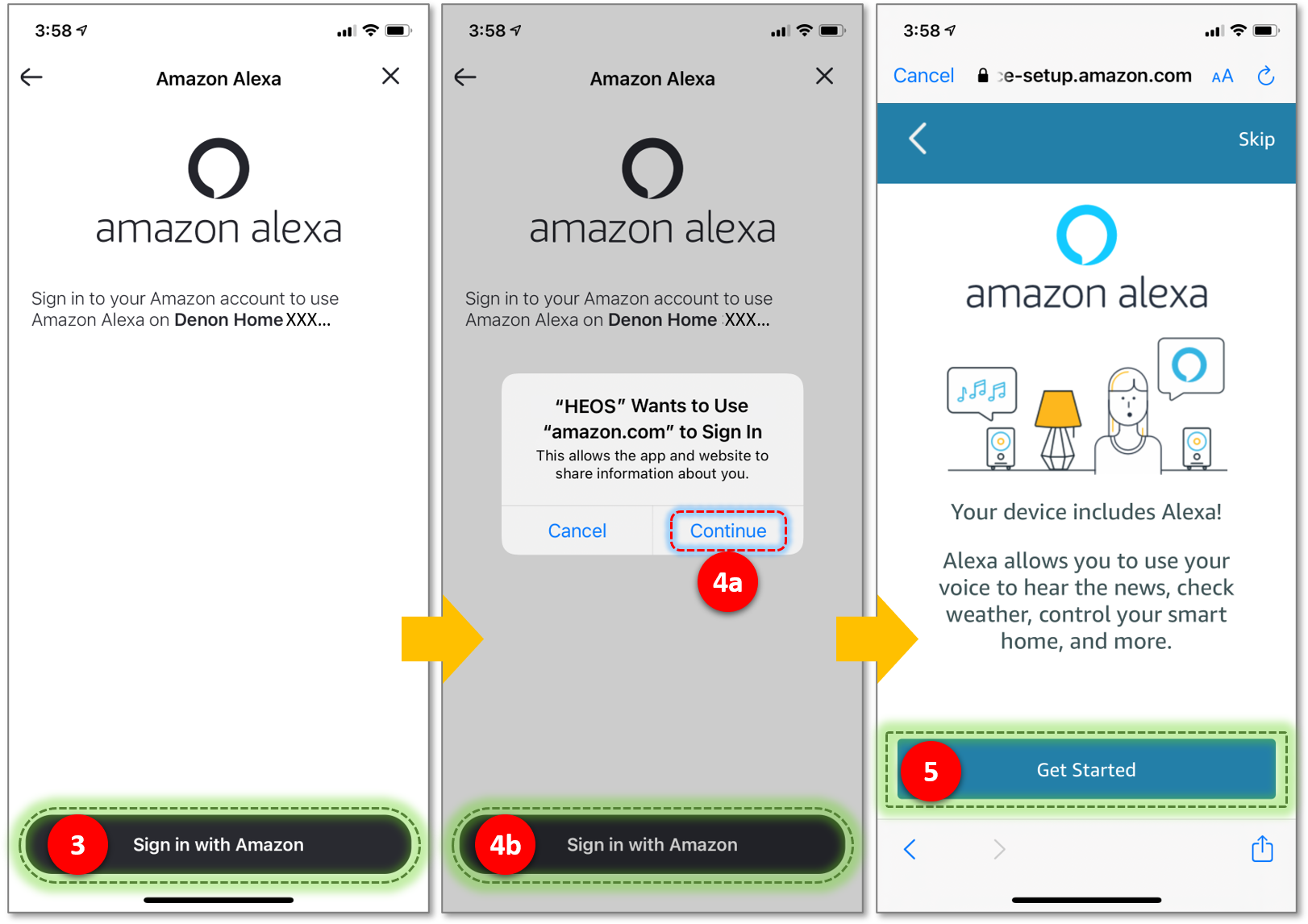
Alexa Account Linking: 5 Steps to Seamlessly Link Your Alexa Skill to User Systems That Require Authentication : Alexa Blogs

Alexa Account Linking: 5 Steps to Seamlessly Link Your Alexa Skill to User Systems That Require Authentication : Alexa Blogs





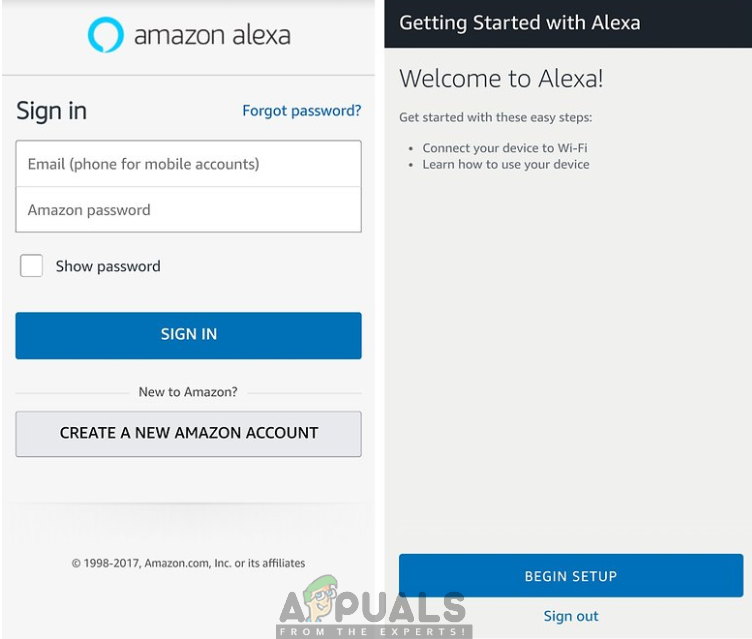
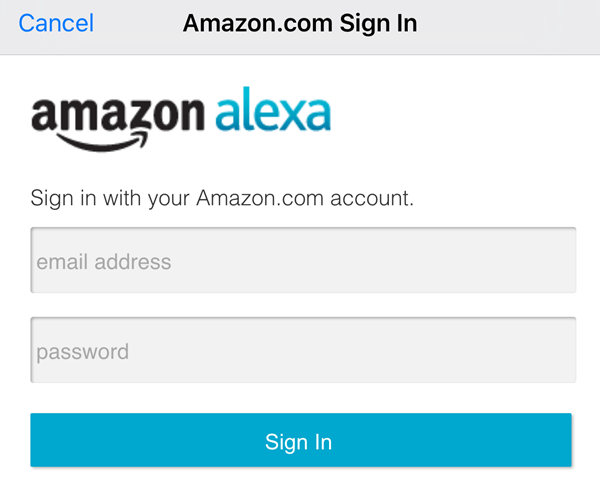
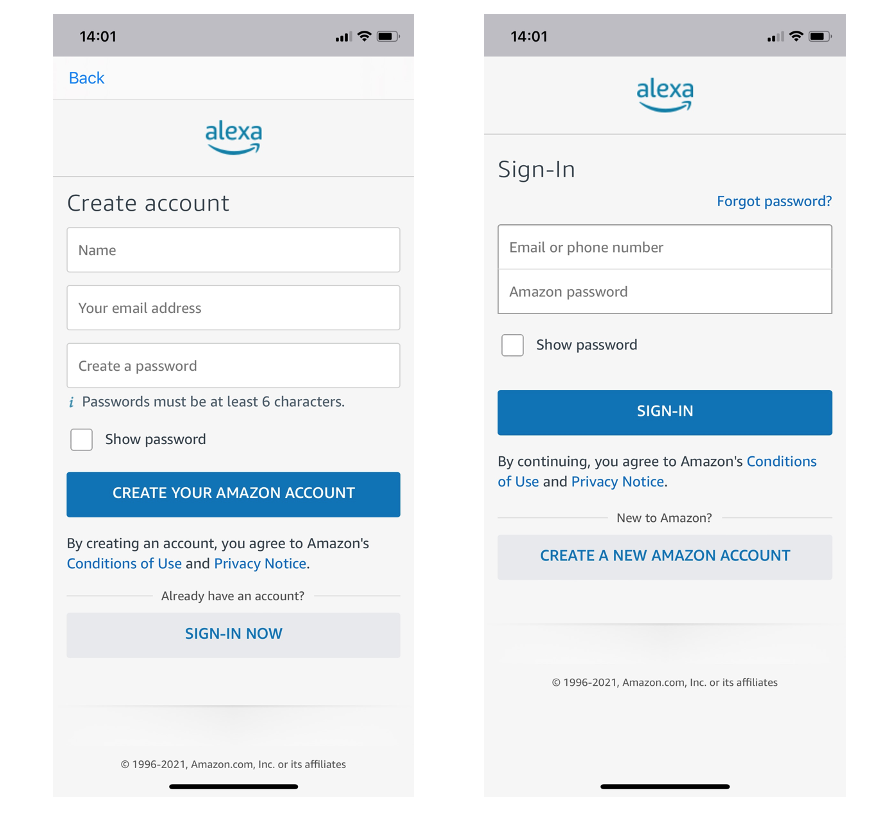
![Tutorial] Account Linking: Getting User's Amazon Email in Alexa Skill Tutorial] Account Linking: Getting User's Amazon Email in Alexa Skill](https://docs.bottalk.de/assets/images/tutorials/alexa-login-with-amazon-email/alexa-login-with-amazon-email-2.jpeg)

![Amazon Echo Won't Connect to Wi-Fi [Quick Fixes] Amazon Echo Won't Connect to Wi-Fi [Quick Fixes]](https://i0.wp.com/www.alphr.com/wp-content/uploads/2020/04/alexashot.jpg?resize=738%2C320&ssl=1)